Quantum Computing Threats: Risks to Encryption and the Path to Post-Quantum Security
Quantum Computing Threats: Because Nothing Says 'Future-Proof' Like Panicking About Schrödinger's Hack
In the rapidly evolving landscape of technology, quantum computing stands out as a double-edged sword. On one hand, it promises breakthroughs in fields like drug discovery, optimization problems, and complex simulations. On the other, it poses an existential threat to the cryptographic foundations that secure our digital world.
As quantum computers advance, they could render many current encryption methods obsolete, exposing sensitive data to unprecedented risks. This blog post explores these threats, including the insidious “harvest now, decrypt later” attacks, and outlines practical steps businesses can take to prepare for a post-quantum era.
The Quantum Threat to Current Encryption Standards
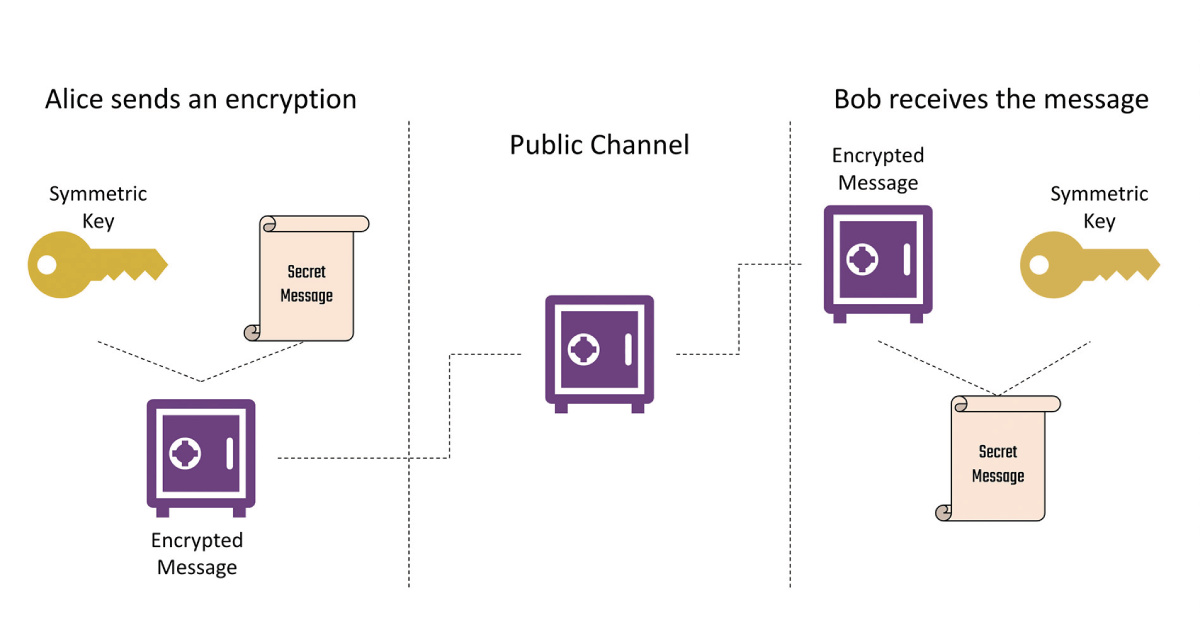
Today’s encryption relies heavily on public-key cryptography systems like RSA (Rivest-Shamir-Adleman) and ECC (Elliptic Curve Cryptography). These algorithms secure everything from online banking transactions to confidential communications by making it computationally infeasible for classical computers to factor large numbers or solve discrete logarithm problems. However, quantum computers operate on principles of superposition and entanglement, allowing them to perform certain calculations exponentially faster.
A key vulnerability stems from Shor’s algorithm, developed in 1994, which enables quantum computers to factor large integers efficiently. For instance, breaking a 2048-bit RSA key, which would take classical supercomputers billions of years, could be done by a sufficiently powerful quantum computer in mere hours or days. Similarly, Grover’s algorithm threatens symmetric encryption like AES by reducing the effective key strength—halving the security of a 256-bit key to 128 bits, though this requires massive quantum resources.
While fault-tolerant quantum computers capable of these feats are not yet here—current systems are noisy and limited to hundreds of qubits—the pace of development is alarming. Experts warn that many organizations underestimate this risk, with quantum advancements potentially breaking existing encryption sooner than expected. The implications are vast: compromised data integrity in sectors like finance, healthcare, and national security.
“Harvest Now, Decrypt Later” Attacks: A Silent Menace
Even without fully realized quantum computers, adversaries are already positioning themselves for future decryption. This strategy, known as “harvest now, decrypt later” (HNDL), involves intercepting and storing encrypted data today, with the intent to crack it once quantum technology matures. It’s a form of long-term surveillance where encrypted communications, financial records, or intellectual property are collected en masse, awaiting the day when algorithms like Shor’s can unlock them.
HNDL is particularly insidious because it exploits the longevity of sensitive data. Information encrypted now might remain valuable for decades—think medical histories or trade secrets. State actors and cybercriminals are suspected of engaging in this practice, as evidenced by reports from organizations like the U.S. Federal Reserve and cybersecurity firms. The attack doesn’t require immediate quantum capability; it’s a bet on future breakthroughs, making it a “silent threat” that’s hard to detect.
This approach amplifies the urgency: data transmitted securely today could be retroactively exposed, leading to widespread breaches. For businesses, this means that procrastination on quantum readiness could result in catastrophic data loss down the line.
Steps Businesses Can Take to Transition to Post-Quantum Cryptography
The good news is that the cybersecurity community is not standing still. Post-quantum cryptography (PQC) refers to algorithms designed to withstand quantum attacks, and standardization efforts are well underway.
The National Institute of Standards and Technology (NIST) has been leading this charge, finalizing its first set of PQC standards in August 2024, with additional selections in 2025. These include:
ML-KEM (FIPS 203): Based on CRYSTALS-KYBER, for key encapsulation.
ML-DSA (FIPS 204): Derived from CRYSTALS-Dilithium, for digital signatures.
SLH-DSA (FIPS 205): From SPHINCS+, a stateless hash-based signature scheme.
HQC: Selected in March 2025 for additional key encapsulation.
Transitioning to PQC requires a strategic approach. Here’s a step-by-step guide for businesses:
Conduct a Crypto Inventory: Map out all cryptographic assets in your systems, including algorithms, keys, and protocols. Identify where RSA or ECC is used and assess the sensitivity of protected data.
Assess Risks and Prioritize Assets: Evaluate the quantum vulnerability of your data. Prioritize high-value assets like long-term secrets or critical infrastructure. Consider the “harvest now” risk for data with extended lifespans.
Build Crypto-Agility: Design systems that can easily switch cryptographic algorithms. This involves adopting hybrid approaches—combining classical and PQC methods during transition—to ensure interoperability.
Test and Prototype PQC Implementations: Start with prototypes in non-production environments. Test NIST-approved algorithms for performance impacts, as some PQC methods require larger keys or more computation.
Align with Vendors and Update Policies: Work with software and hardware vendors to ensure PQC support. Update security policies, train staff, and monitor for new standards or threats.
NIST emphasizes that preparation must begin now, as full deployment could take decades, mirroring the rollout of modern cryptography. Resources like the NCCoE’s migration projects provide practical demonstrations.
TLDR: Act Now to Secure Tomorrow
Quantum computing’s threat to encryption is not science fiction—it’s a looming reality that demands proactive measures. By understanding risks like HNDL attacks and embracing PQC, businesses can safeguard their data against future quantum adversaries. The transition won’t be overnight, but starting today ensures resilience in an uncertain digital future. Stay informed, assess your posture, and collaborate with experts to navigate this quantum shift.